
[ad_1]

PhD scholar Asmit Nayak is investigating ways in which browser extensions might extract passwords and different delicate information from standard web sites. Nayak, together with fellow PhD scholar Rishabh Khandelwal and Kassem Fawaz, a UW–Madison affiliate professor {of electrical} and laptop engineering, first found the difficulty whereas investigating Google login webpages. Photograph By: Joel Hallberg
While you sort a password or bank card quantity into an internet site, you count on that your delicate information will probably be protected by a system designed to maintain it safe.
That’s not all the time the case, in line with a bunch of digital safety researchers on the College of Wisconsin–Madison. They discovered that some standard web sites are susceptible to browser extensions that may extract consumer information like passwords, bank card data and social safety numbers from HTML code. A preprint of their work has already created a buzz in tech circles.
The workforce contains Rishabh Khandelwal and Asmit Nayak, PhD college students who work with Kassem Fawaz, a UW–Madison affiliate professor {of electrical} and laptop engineering. The trio first found the difficulty whereas investigating Google login webpages.
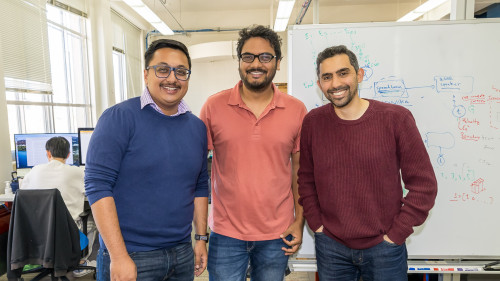
PhD college students Asmit Nayak (left) and Rishabh Khandelwal (middle) and Electrical and Pc Engineering Affiliate Professor Kassem Fawaz started investigating browser extension safety after they discovered passwords displayed in plain textual content whereas trying on the login pages of standard web sites. Photograph By: Joel Hallberg
“We had been simply messing round with login pages, and within the HTML supply code we might see the password in plain textual content,” says Nayak. “We thought, ‘That is attention-grabbing. Why is that this occurring? Is it doable that different web sites are doing one thing related?’ Then we began digging deeper.”
They found an enormous subject. The researchers discovered that a large variety of web sites — about 15% of greater than 7,000 they checked out — retailer delicate data as plain textual content of their HTML supply code. Whereas many safety measures preserve hackers from accessing this information, the workforce hypothesized that it could be doable to search out it utilizing a browser extension.
Browser extensions are add-ons that, utilizing small bits of code, permit customers to customise their web expertise, for instance by blocking advertisements or bettering time administration. Browser builders generally introduce experimental options by way of extensions whereas additionally permitting third-party builders to supply their very own extensions for customers to strive. The researchers discovered {that a} malevolent extension might use code written in a typical programming language to seize customers’ login data, passwords and different protected information.
“Combining what we learn about extensions and about web sites, an extension can very simply entry customers’ passwords,” says Fawaz. “It’s not one thing that really is going on, however there may be nothing stopping it.”
Surveying the extensions accessible for the Google Chrome browser, the workforce discovered that 17,300, or 12.5% of the accessible browser extensions, had the mandatory permissions to use this vulnerability. To see if it was possible for such an extension to make it into circulation, they developed their very own extension and submitted it to the Chrome Net Retailer, describing it as an AI assistant providing ChatGPT-like capabilities on web sites. The shop accepted the extension. The workforce was cautious to not launch the extension to the general public and rapidly deleted it after it was accepted, demonstrating that it was doable for such an exploit to get in beneath the radar. The researchers emphasize that at no level was there any hurt to customers.
Khandelwal says that almost certainly an actual hacker wouldn’t comply with the identical path.
“Any individual who’s malicious doesn’t want to start out from scratch,” he says. “They will get entry to current extensions, for example, by shopping for one with a number of customers and tweaking the code a bit of bit. They may keep the performance and get entry to the passwords very simply.”
Fawaz says it’s possible that the vulnerability isn’t an oversight; as an alternative, browser safety is configured this technique to let standard password supervisor extensions entry password data. For its half, in a press release to the researchers, Google says that it’s trying into the matter however doesn’t take into account this a safety flaw, particularly if permissions for the extensions are configured accurately.
Fawaz, nonetheless, remains to be involved, and he hopes his analysis will persuade web sites to rethink the way in which they deal with this delicate data. His workforce proposes alerts to let customers know when delicate information is being accessed by browser extensions, in addition to instruments for builders to guard these information fields.
“It’s a harmful factor,” Fawaz says. “That is one thing that individuals actually need to know: Passwords aren’t all the time secure on browsers.”
[ad_2]